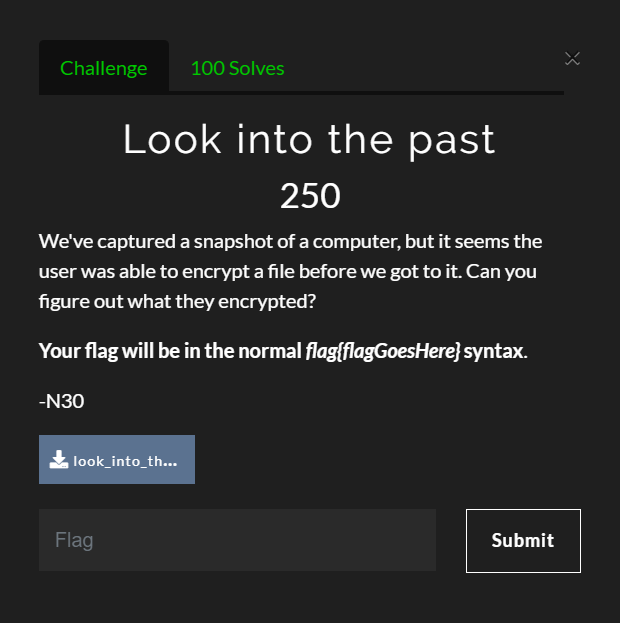
Look Into the Past was a fun challenge that gave players a zipped copy of a Linux machine's file system. The goal of this challenge was to find the flag placed in an encrypted file.
Accessing the Challenge
First, I downloaded the file from the CTF site and extracted it.
tar -zxvf look_into_the_past.tar.gzGetting Started
My first thought after reading the challenge description was to find out which file had been encrypted. I assumed a user encrypted the file; therefore, the command would likely exist is the user's BASH history file. Which user though?
First, I changed into the home directory to see which users had home directories on the system.
cd look_into_the_past/home/
ls -l
total 4
drwxr-xr-x 9 1000 1000 4096 Feb 8 21:20 UserThankfully, there was just one user: User. I then looked to see if they had a BASH history file.
ls -la User/total 56
drwxr-xr-x 9 1000 1000 4096 Feb 8 21:20 .
drwxr-xr-x 3 1000 1000 4096 Feb 8 10:24 ..
-rw-r--r-- 1 1000 1000 349 Feb 6 12:33 .bash_history
-rw-r--r-- 1 1000 1000 864 Feb 6 12:34 .bashrc
drwxr-xr-x 2 1000 1000 4096 Feb 8 10:24 Desktop
drwxr-xr-x 2 1000 1000 4096 Feb 8 21:23 Documents
drwxr-xr-x 2 1000 1000 4096 Feb 8 10:24 Downloads
drwxr-xr-x 2 1000 1000 4096 Feb 8 10:24 Music
drwxr-xr-x 2 1000 1000 4096 Feb 8 10:24 Pictures
-rw-r--r-- 1 1000 1000 672 Feb 6 12:34 .profile
drwxr-xr-x 2 1000 1000 4096 Feb 8 10:24 Public
-rw-r--r-- 1 root root 11 Feb 8 21:20 steganopayload213658.txt
drwxr-xr-x 2 1000 1000 4096 Feb 8 10:24 VideosI looked into the .bash_history file and saw the following content.
cd Documents
openssl enc -aes-256-cbc -salt -in flag.txt -out flag.txt.enc -k $(cat $pass1)$pass2$pass3
steghide embed -cf doggo.jpeg -ef $pass1
mv doggo.jpeg ~/Pictures
useradd -p '$pass2' user
sqlite3 /opt/table.db "INSERT INTO passwords values ('1', $pass3)"
tar -zcf /opt/table.db.tar.gz /opt/table.db
rm $pass1
unset $pass2
unset $pass3
exitLooking at this output, the user used openssl to encrypt the file using three variable: $pass1, $pass2, and $pass3.
Finding $pass1
Reading the BASH history, I could tell that $pass1 was a file given that the password used cat on the variable to read its content for the openssl password. Then, it was embedded in a file named doggo.jpeg, which was moved into the Pictures directory.
I tried various passphrases at first using steghide to extract the file from doggo.jpeg, all to no avail. Finally, I tried using steghide without a passphrase and it worked!
steghide extract -sf User/Pictures/doggo.jpeg
Enter passphrase:
wrote extracted data to "steganopayload213658.txt"Reading the contents of the file gave me the value of $pass1: JXrTLzijLb
cat steganopayload213658.txt
JXrTLzijLbFinding $pass2
Next, I proceeded to find $pass2. According to the BASH history, $pass2 was used as a password during the creation of a new user. If you read the help content for useradd, it'll say that the -p option is used to provide an encrypted password of a new account. This means that whatever value you give for the password is assumed to already be encrypted. The password is then stored in /etc/shadow for the user.
I read the contents of the shadow file; the password is stored after the username and delimited by colons.
cat ../etc/shadow
...
user:KI6VWx09JJ:18011:0:99999:7:::The password for user - and the value of $pass2 - was KI6VWx09JJ.
Finding $pass3
Now onto the last variable. According to the BASH history, the value of this variable was inserted into table.db in the opt directory. The file was then compressed using tar.
First, I copied the tar file into the /tmp directory and extracted it.
cp ../opt/table.db.tar.gz /tmp
cd /tmp
tar -zxvf table.db.tar.gzNow with the database file extracted in the /tmp directory, I used sqlite3 to query the database.
sqlite3 table.dbsqlite3> SELECT * FROM password;
1|nBNfDKbP5nThere we have it; $pass3 was nBNfDKbP5n. Now, I had all the pieces to decrypt the file and find the flag.
Decrypting the Flag File
I knew from the BASH history that the password was a concatenation of $pass1, $pass2, and $pass3, making the password JXrTLzijLbKI6VWx09JJnBNfDKbP5n.
I used openssl to decrypt the file and find the flag.
openssl enc -aes-256-cbc -d -in flag.txt.enc -out flag.txtWhen prompted, I gave the password: JXrTLzijLbKI6VWx09JJnBNfDKbP5n. The decrypted file flag.txt appeared. Reading the contents of the file gave me the flag.
flag{h1st0ry_1n_th3_m4k1ng}Conclusion
This challenge was a lot of fun. I'm not sure that I would ever expect to see anyone secure their files in this manner by splitting up the password; nonetheless, it was a lot of fun to tackle.


